Browser Forensics Just Got Way Easier — And It's Free
- Mar 7
- 2 min read

Okay let me be real with you for a second.
Browser forensics manually? It's a pain.
You're digging through SQLite databases, remembering artifact locations, writing queries — and if you're doing it with free tools, it only gets worse.
I actually built a full series on how to do this manually if you want to go deep on it — link here:
But today? I found a tool that makes all of that dramatically simpler. And it pairs beautifully with KAPE, which if you know me, you know I love.
-------------------------------------------------------------------------------------------------------
Step 1 — Collect Your Artifacts With KAPE
Before the tool does anything, you need to actually collect the browser artifacts off the system. KAPE handles this perfectly. If you're running PowerShell:
If you prefer the GUI, even easier — just tick WebBrowsers as your target.

-------------------------------------------------------------------------------------------------------
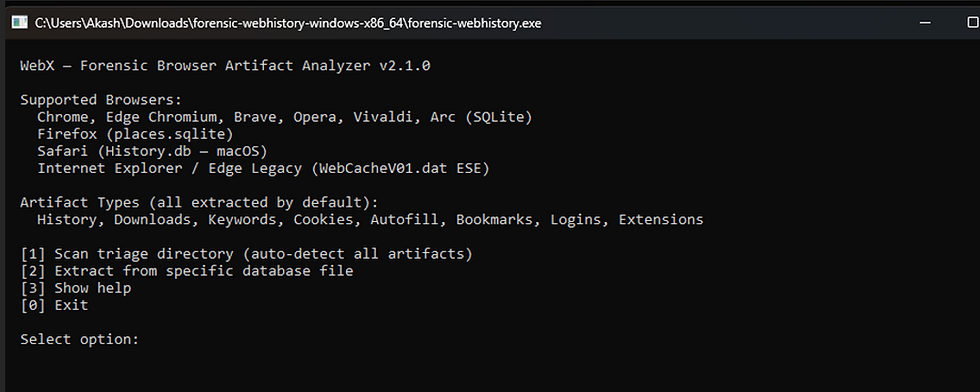
Step 2 — Meet the Tool
Drum roll... 🥁
That's it. That's the tool. And I genuinely love it.
What makes it special? You can run it on Windows, WSL, Linux, or Mac. Doesn't matter where the evidence came from — Mac, Windows, whatever — the tool just reads the SQLite files directly. Cross-platform by nature.
-------------------------------------------------------------------------------------------------------
Running It on Windows
Download the executable, run as Administrator, and you get this menu:
Select 1, point it at your KAPE output folder, choose where you want results saved, hit enter — done.
About a minute later you have a clean Excel output. That's it. No SQL queries, no manual path hunting.

Output! (Analyse all the output with my another favorite tool Timeline explorer)

-------------------------------------------------------------------------------------------------------
What Browsers Does It Support?
-------------------------------------------------------------------------------------------------------
Bonus — Parsing Mac Evidence on WSL
This is where it gets cool. I had a Mac artifact set collected using UAC (Unix Artifact Collector) and I wanted to parse it on Windows via WSL2.
Here's the exact command I ran:
MAC output in excel

-------------------------------------------------------------------------------------------------------
Why I Actually Like This Tool
Look, paid tools like Magnet AXIOM or Cellebrite make this trivial — but they cost money, sometimes a lot of it.
This tool gives you clean Excel output, covers every major browser, runs cross-platform, and pairs with KAPE out of the box.
For anyone doing DFIR on a budget or just learning the craft, this is genuinely one of the best free tools out there right now.
Go try it. You'll get it immediately.
-------------------------------------------------------------------------------------------------------
If this helped — share it, react, drop a comment. More coming.
-----------------------------------------------Dean----------------------------------------------





Comments