

My Mission
To make practical cybersecurity knowledge accessible, understandable and actionable.

Ready to join me in Cybersecurity Journey ?

Tools Expertise
EDR / MDR : SentinelOne (MDR), Qualys EDR, MDFE, Carbon Black
XDR : Bitdefender, CrowdStrike Falcon
CDR : Obsidian
SIEM : Microsoft Sentinel (IR purposes), Panther
Email EDR : Sublime Security
Identity Sec : Petra Security
Log Analysis : Chainsaw, Hayabusa, LogParser, EvtxECmd
DFIR : Velociraptor, Redline, FTK Imager, Cyber Triage,
DFIR : OSForensics, Magnet AXIOM, Belkasoft
Memory : Volatility 3, WinPmem, MemProcFS
File Recovery : PhotoRec
Eric Tools : KAPE, AmcacheParser, ShimCacheParser, JLECmd,
Eric Tools : LECmd, SBECmd, Registry Explorer (All tools)
Timeline : MFTECmd, Log2Timeline (Plaso)
Microsoft 365 : Microsoft Extractor Suite, Analyzer Suite
Project:
CE SentinelOne Assistant : https://s1copilot.onrender.com/

Quick Guides (Created by me)
Intrusion detection Cheat sheet
Incident Handling Checklist
FTK Imager Based Imaging
Windows Artifact Analysis
Post-Attack Remediation Steps
for Windows, Linux, Mac:
Linux IR Cheatsheet
Common (Win) Artifact Paths

Important Registry Collection
Lateral Movement Analysis
USB Forensic
Email Analysis
Incident response/analysis script created by me
Threat Intelliegnce for Ransomware DLSs
MAC IR Cheatsheet
Curriculum Certifications
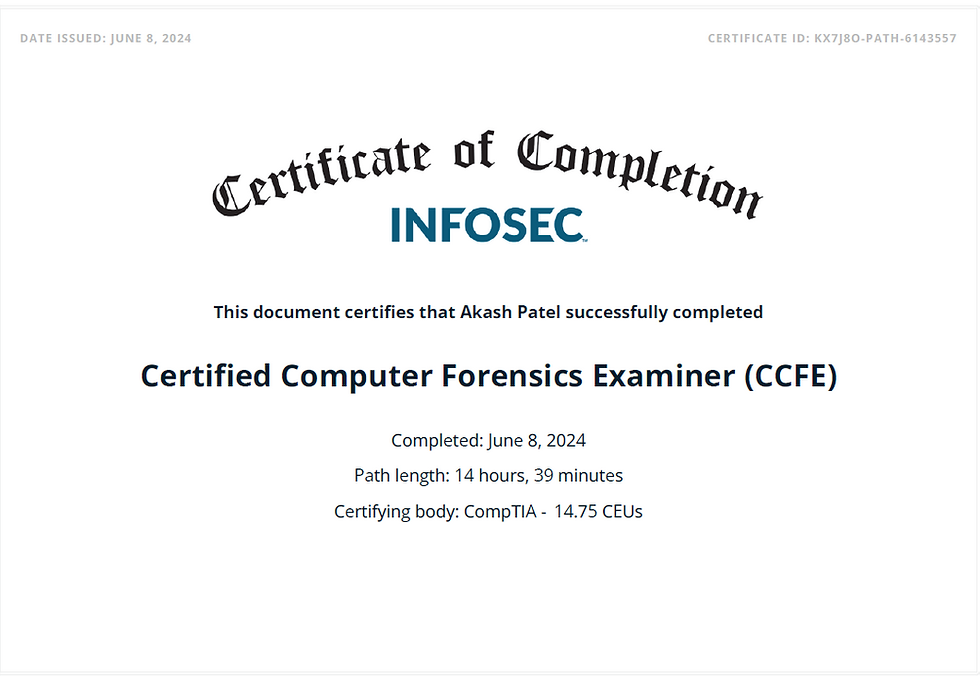


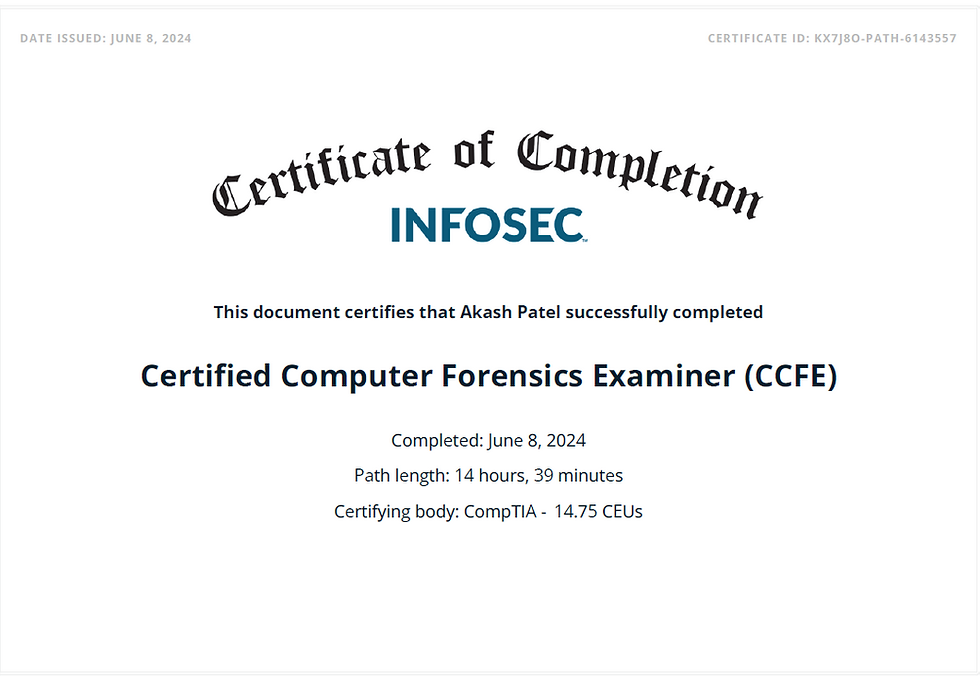
Professional Credentials

Windows Forensic certification from Belkasoft



Windows Forensic certification from Belkasoft

Professional Endorsement


Designation :- Cyber - Operation Executive
05/2021 -09/2022

Designation :- Cyber Security Analyst L2
09/2022 - 05/2024

Designation :- Cybersecurity Incident response, Associate
05/2024 - 07/2025

Designation :- CERT (Incident Response and Digital Forensic)
09/2025 - Present
Ready to discuss:
- Schedule a call for a consultation
- Message me via "Let's Chat" for quick questions
Let's connect!